Nov. 18, 2025
A consolidated overview of real-world vulnerabilities identified across web and API assessments
binsec GmbH has consolidated the results of all web penetration tests (including connected APIs) conducted over the past twelve months. The data provides a clear picture of the vulnerability categories that appear most frequently in practice.
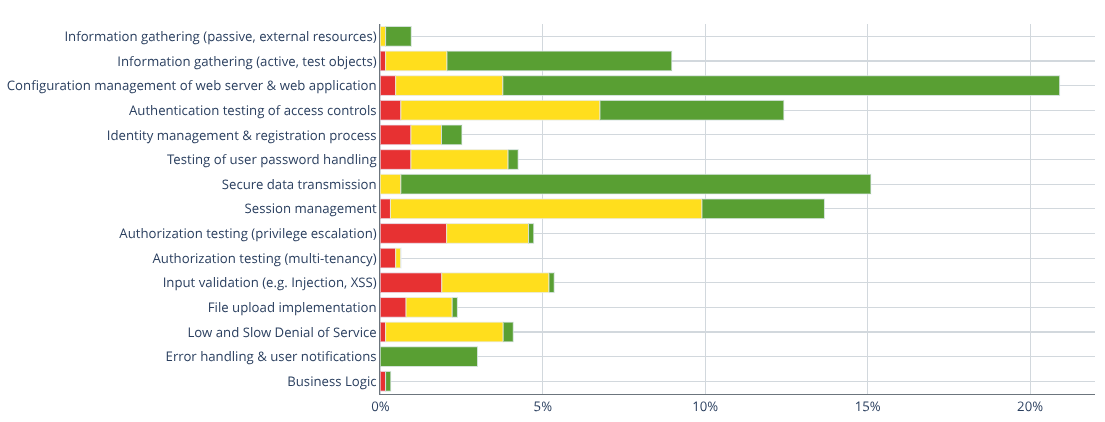
A significant portion of the findings relates to basic configuration weaknesses, such as insecure web server defaults, missing security headers, or inadequately configured TLS parameters. These issues are easy to identify and typically do not represent an immediate critical risk.
Session ManagementSession handling weaknesses continue to occur regularly. A common pattern is that logging out removes the session only in the browser, while the server-side session remains active. This allows continued use of a previously compromised session.
Authorization and Access ControlMost critical findings stem from incomplete or faulty access control mechanisms. This includes privilege escalation paths, missing object- or tenant-level isolation, and insufficient protection of API endpoints. Modern applications with extensive background API communication are particularly affected, as access controls often need to be implemented manually.
Classic VulnerabilitiesSQL injection and cross-site scripting (XSS) are less common today but still appear in practice – especially in areas where safeguards such as ORMs, input validation, or prepared statements are bypassed or not applied consistently.
Business Logic IssuesBusiness logic vulnerabilities occur infrequently, but when identified, they typically have a significant impact because they directly affect critical application workflows.
Talk now
to our
Pentest experts.
Contact us

OSCP, M.Sc. Security Management
Talk now to our Pentest experts.

OSCP, M.Sc. Security Management
Manual Penetration Testing by Certified, In-House Senior Penetration Testers

Who tests
For more than ten years, binsec has stood for technically rigorous, strictly manual penetration testing. All engagements are conducted exclusively by employed senior penetration testers. Freelancers or subcontractors are not involved. Our clients work directly with the responsible senior tester who personally performs and technically leads the assessment. Communication is conducted in German and English; international projects are a regular part of our work. Our experts hold recognized offensive security certifications such as OSCP, OSCE, CRTO, and BACPP.
What we test
Our project experience covers complex enterprise networks, modern web and API architectures, and hybrid infrastructures. We work with organizations in manufacturing and industry, financial services and insurance, healthcare, IT and software providers, as well as public institutions. Technical, regulatory, and organizational requirements are systematically taken into account.
How we work
Our tests are based on a structured and reproducible methodology. They align with established standards such as OWASP and OSSTMM and are adapted to the specific project scope. Each assessment follows clearly defined phases: structured reconnaissance, manual analysis, targeted exploitation, and validated impact assessment. Automated tools support the process; identification, verification, and evaluation of vulnerabilities are performed manually.
Where we operate and document
Assessments are not conducted from cloud infrastructures. We operate our own infrastructure in a data center in Frankfurt. From there, all engagements are centrally executed and documented within our internal system PTDoc. PTDoc serves as the central documentation platform for all project data, evidence, and evaluations. All findings are recorded in a structured manner, technically described, risk-assessed, and supported by reproducible proof-of-concept information.
What you receive
We identify technical vulnerabilities and assess their business impact. Findings are evaluated based on risk or CVSS. The result is a clearly structured report including an executive management summary and detailed technical documentation. Re-testing of identified vulnerabilities is an integral part of our service.

 +49 692475607-0
+49 692475607-0