
For an international stockbroker, we tested a trading platform providing real-time data via WebSockets. In addition to the mobile app, a dedicated TAN app for transaction authorization was examined. The focus was on authentication, transaction integrity, and protection of sensitive customer data.

At several schools, IT infrastructures were assessed remotely via PenPIs. The focus was on separated network segments and distinct Active Directory domains for staff and students. The aim was to verify segmentation and protection of sensitive data.

Municipal applications such as administrative software, citizen apps, vaccination coordination, and vehicle registration systems were tested. The assessments focused on manipulation resistance, role models, and exposed interfaces. The aim was to secure sensitive citizen and government data.

Business intelligence solutions in real estate and Microsoft PowerBI integrations were tested. The focus was on preventing data manipulation or unauthorized access. The goal was to protect critical analytics and decision-making processes.

APIs for issuing and verifying digital identity credentials were tested. The focus was on OIDC4VCI, OIDC4VP, and SD-JWT standards. The aim was to ensure forgery-resistant credentials.
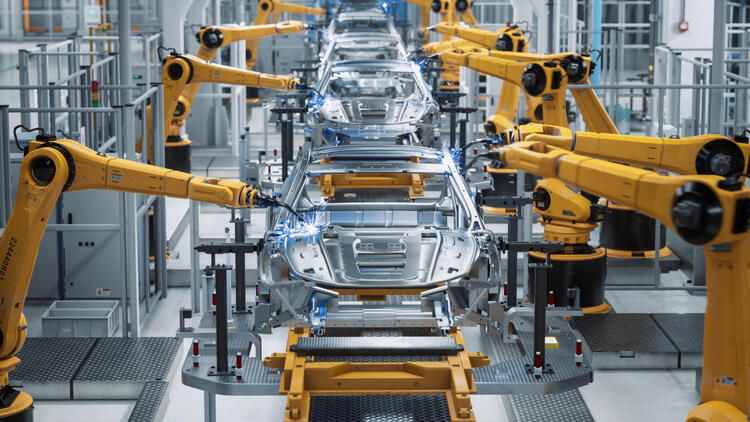
A platform processing Lidar sensor data for AI training in autonomous driving was tested. The assessments followed TISAX requirements. The focus was on protecting sensitive development data.

An online pharmacy with user, doctor, and admin roles was tested. Prescriptions and orders are handled via a workflow framework. Role models, workflows, and data security were examined.

We assessed DiGA apps in digital psychotherapy. Tests included source code and data storage on mobile devices. The goal was to protect sensitive patient data.

A platform with chatbots, voicebots, and LLM integration was tested. Assessments focused on communication and workflow transitions. The goal was secure handling of customer data.

APIs for managing car insurance and claims were tested. Authentication, input validation, and confidentiality were key focus areas. The goal was to protect sensitive customer data.
We tested several web applications developed using the Google Web Toolkit (GWT), often found in administrative environments. GWT penetration tests are technically demanding because communication and data structures are proprietary rather than standard REST or JSON interfaces.

We tested HR solutions for recruiting, employee management, and corporate pension schemes. The scope included virtual assessment centers, survey workflows with AI-based evaluation, and processes such as onboarding/offboarding and reference generation.

We assessed a P2C platform for centralized product maintenance, a shop with a members area for physical and digital goods (including passwordless login), and a shipping solution integrating multiple carriers with automated label generation.

We assessed an open-source vector database offered as SaaS. Full access to the source code enabled in-depth analysis. The goal was to identify vulnerabilities in complex APIs and data structures.

We tested single sign-on solutions based on OAuth and OIDC. Both standard products such as Keycloak and custom implementations were included. The goal was to secure authentication and access control.

We tested an affiliate marketing platform and a social media management solution. The focus was on interfaces integrating external content. The goal was to mitigate manipulation and malicious code risks.

A CRM system for the logistics sector was tested. Focus areas were functionality, tenant separation, and data security. The goal was to prevent unauthorized cross-customer access.

A SaaS solution for fleet management and route optimization was tested. A proprietary binary format was used for communication and storage. The goal was to analyze authorization and input validation.

Various MedTech solutions were tested, including AI-based diagnostics, implants with RF communication, and apps for sleep diagnostics. The focus was on data and device security. The aim was to protect sensitive patient data.

A multi-tenant property management solution was tested. The focus was on tenant separation and communication features. The aim was to secure confidential data between administrators, tenants, and service providers.

A hospital network with multiple sites was tested. The analysis covered patient data, building control, and emergency systems. The aim was to secure critical healthcare infrastructure.

A chemical company was tested for both IT and physical security. In addition to internal and external IT tests, real intrusion scenarios were simulated. The goal was to obtain a comprehensive view of potential attack vectors.

binsec regularly tests universities external services and internal networks. A key focus is safeguarding student and staff data. Reviews of Moodle instances and connected systems are also a common part of the penetration test.

Penetration tests in financial environments are complex. They require broad testing across online banking, mobile apps, and APIs. High software quality makes findings rare. When vulnerabilities are found, they underscore the value of experience and a structured approach.

As an international standard for medical imaging, DICOM defines the formats for medical images and ensures that they can be exchanged with the required data and in the required quality for clinical use.

During the pentest of a booking portal for an international travel agency, we had to pay particular attention to the relevant limitations during the test.

Licensed online sports betting providers are subject to special regulatory requirements that may also affect a penetration test.

Pentesting payment APIs is a typically assignment, we did countless times. Even if the basis is checking against OWASP Top 10, we still take a look on more logical security topics, too.

We regularly receive customer inquiries who would like to have their publicly accessible IT checked for vulnerabilities. In the case of very large IP networks, this can get difficult in terms of time.

 +49 692475607-0
+49 692475607-0