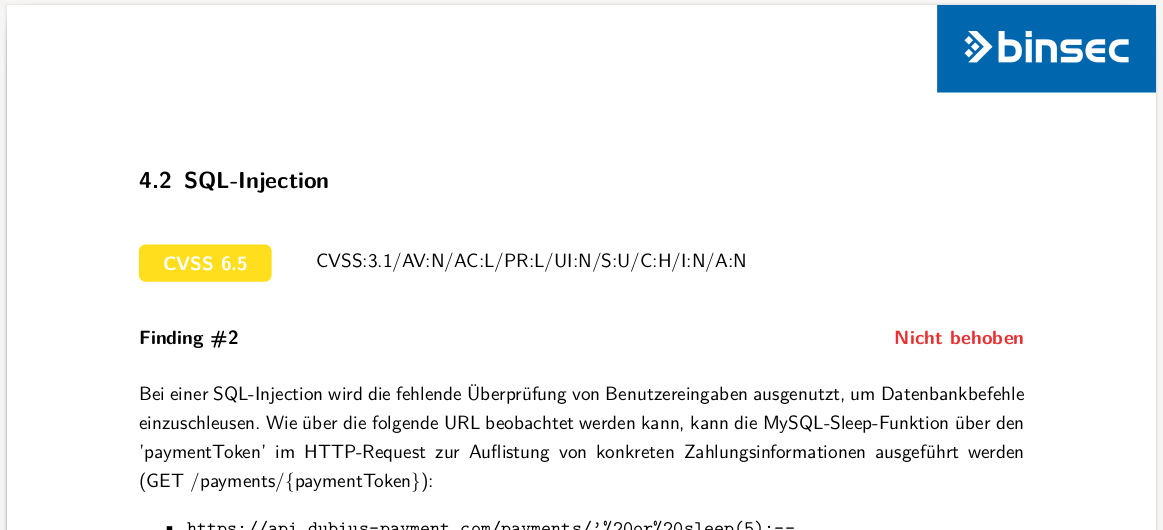
CVSS (Common Vulnerability Scoring System)
The following screenshot is an example of a CVSS rating for an SQL Injection resulting in a CVSS score of 6.5:
Your advantages with
binsec GmbH
As an owner-managed pentest boutique – staffed by a high-performing team of around 10 experienced senior experts – binsec GmbH has specialized in sophisticated penetration testing for over a decade. We demonstrate our deep roots in the community every day through our own platforms like binsec.tools, binsec.wiki, and binsec.academy. Relevant academic degrees, high-caliber industry certifications, and years of hands-on project experience are what truly matter to us – and how we guarantee a precise, manual analysis for every assessment.
Contact usMore than 10 years of practical experience in penetration testing
No subcontractors or external freelancers
Direct communication with the responsible senior penetration tester
Structured, documented, and reproducible testing methodology based on PTDoc®
Fully controlled in-house pentesting infrastructure, no cloud services used
Identification of technical and business-relevant security risks
Risk-weighted vulnerability assessment or CVSS based scoring
Report including executive summary and detailed technical section
Retesting of identified vulnerabilities included
Your advantages with
binsec GmbH
As an owner-managed pentest boutique – staffed by a high-performing team of around 10 experienced senior experts – binsec GmbH has specialized in sophisticated penetration testing for over a decade. We demonstrate our deep roots in the community every day through our own platforms like binsec.tools, binsec.wiki, and binsec.academy. Relevant academic degrees, high-caliber industry certifications, and years of hands-on project experience are what truly matter to us – and how we guarantee a precise, manual analysis for every assessment.
More than 10 years of practical experience in penetration testing
No subcontractors or external freelancers
Direct communication with the responsible senior penetration tester
Structured, documented, and reproducible testing methodology based on PTDoc®
Fully controlled in-house pentesting infrastructure, no cloud services used
Identification of technical and business-relevant security risks
Risk-weighted vulnerability assessment or CVSS based scoring
Report including executive summary and detailed technical section
Retesting of identified vulnerabilities included
Pentest-Methodology
A penetration test is a structured attack on IT systems or applications to identify potential vulnerabilities. It uses the same tools and techniques that real attackers would use to break into a system. Thus, a penetration test is not an automated vulnerability scan. On the contrary, a penetration test as a service is always a combination of using security tools and conducting manual tests to uncover vulnerabilities. While a real attacker only needs to find and exploit a single vulnerability, a penetration tester checks all relevant attack vectors.
Having a structured approach is one of the most important factors For this purpose, we use our own platform PTDoc®, a specialized pentest documentation tool that logs all manual testing steps in full compliance with all relevant security standards and translates them into a clear, reproducible report for you. Since this tool significantly reduces the overhead of report generation, it allows us to focus entirely on our core mission as pentesters: identifying and analyzing critical security flaws. to achive this in order to provide a professional pentesting service. Our approach is based on all relevant standards and publications.
How We Work
From Planning to Re-Testing
Preparations
We coordinate the technical and organisational framework for the penetration test, communication channels, points of contact and testing windows. Depending on the project, this is done through a kick-off meeting or a brief exchange via e-mail. Where required, the client provides relevant technical documentation and access to the systems within scope.
Conducting
The penetration test is performed using a structured and risk-oriented assessment approach that combines automated analysis techniques with extensive manual testing. The specific test cases and assessment procedures depend on the actual conditions, technologies and attack surface encountered within the target environment.
Reporting
After the assessment, we prepare a detailed report including an executive summary, risk ratings, technical details and remediation recommendations. Findings are documented in a clear and reproducible manner and critical issues are communicated immediately during the engagement if required.
Debriefing
We are happy to review the findings and recommendations together with your team. During the debriefing, we explain technical details, potential impacts and remediation priorities, while answering questions and discussing next steps.
Re-Testing
After remediation, we verify whether the identified findings have been successfully resolved and update the report accordingly. Re-testing is generally included for remote assessments and provides assurance that the implemented measures are effective.
Getting an Offer for a pentest with CVSS Report Rating
Pentest are always a compromise between effort and cost, to get a reasonable price. Successful pentest offer a good balance between these criteria to facilitate the testing of all relevant attacks and attack vectors. The cost of such a test always depends on the time the penetration tester spends and on the extent and complexity of the IT system or web applications. While a penetration test for a small application takes only some days, it can take several weeks for a large network or complex application.
For a pentest offers we do require prior information about the systems and applications that are to be examined. It is important that we get an initial impression of the target. For web applications, for example, test access can be helpful. Any additional information, e.g. the framework etc., can make it easier for us to draft a suitable offer for you. If you need us to pentest an IT system, we will need the corresponding network addresses in advance. In this particular case, we will first perform a non-invasive network scan to get a first look at your network. We will provide a detailed offer once we can estimate the effort required.
binsec GmbH is a german pentest company for professional penetration testing. Get in touch with us for your pentest offer with CVSS Report Rating - get your pentest today!
Contact us
Pentesting
for specific standards and requirements
There are a lot of standards or legal requirements worldwide, that require conducting of a penetration test.
binsec GmbH for professional Penetration Testing
Your pentest experts!
binsec GmbH is the german professional penetration testing company. Get a pentest offer without typical sales nonsense. Talk to experts instead to pre sales consultants. Better pentesting. No nonsense. As a professional penetration test provider we do some things differently than other pentest provider: As a penetration test firm, we do not sell vulnerability scans as pentest. We do also focus on business security risks. You are looking for a professionally conducted penetration tests? Get the binsec team for your pentest!
Contact us
Frequently Asked Questions
It is difficult to give an generalized answer to this question, since the toolset used basically depends on the respective test object. Of course, we use tools such as nmap to check IT infrastructures or the Burp Suite Professional in the case of web applications.
However, we believe that publishing a tool list is mere window dressing, as each target system should be tested individually. However, you are welcome to ask us about the tools we used after the pentest.
Hosting critical business applications on a cloud provider such as Amazon AWS, Microsoft Azure, Google Cloud or Hetzner Cloud is becoming increasingly common.
Of course we perform penetration tests for applications hosted in the cloud. This also applies to penetration testing of cloud-based IT infrastructures, provided that the virtual machines are not managed directly by the cloud provider.
We perform penetration tests for almost any IT environment, system, application or network – right down to protocol fuzzing. Only the analysis of hardware chips under a microscope is something we leave to others.
Typical targets of our penetration tests include:
Web Applications and APIs
Mobile Applications
Servers, Platforms and Infrastructure
- Webserver Pentesting
- Network Pentesting
- Firewalls Pentesting
- WiFi / WLAN Pentesting
- Active Directory (AD) Pentesting
- RDP Server / Remote Desktop Pentesting
- OT Pentesting
Containers and DevOps
Identity and Authentication

 +49 692475607-0
+49 692475607-0